
I Tested 10 API Security Best Practices on a Real API and Here Are the Results (2026)
Have you ever wondered what happens when the digital bridges connecting your application to the world are left unguarded?
Imagine spending months meticulously designing a beautiful user interface, crafting an engaging brand identity, and developing a seamless user experience, only to lose it all in an instant. Your product launches, users love it, and growth accelerates until a massive data breach occurs on a random Tuesday. This catastrophe rarely happens because a hacker guessed an admin password; rather, it happens because a single Application Programming Interface (API) endpoint leaked your entire customer database to an automated script. As a multidisciplinary professional bridging the gap between system architecture, cybersecurity, and UI/UX design, I see this silent threat destroy promising businesses all the time.
To move beyond theoretical advice and generic warnings, I decided to put modern API security to the test:
- The Vulnerability Reality: In 2026, APIs act as the nervous system of digital products connecting apps to databases, payment gateways to carts, and AI to CRMs yet they remain one of the most misunderstood and poorly secured attack vectors.
- The Live-Fire Methodology: I set up a real-world, production-grade API sandbox, purposefully left it vulnerable, and subjected it to a barrage of modern, AI-driven cyber attacks.
- The Systematic Defense: Following the initial simulated breaches, I systematically applied 10 industry-standard API security best practices to measure their actual effectiveness against live threats.
- The Target Audience: This article is not a generic IT checklist; it is a documented field test built specifically for startups, business owners, and product teams making high-level architectural decisions.
- The Ultimate Goal: By sharing these results, I want to show you exactly how deeply secure backend architecture is tied to protecting your brand’s reputation, maintaining user trust, and defending your bottom line.
Why This Problem Matters for Businesses
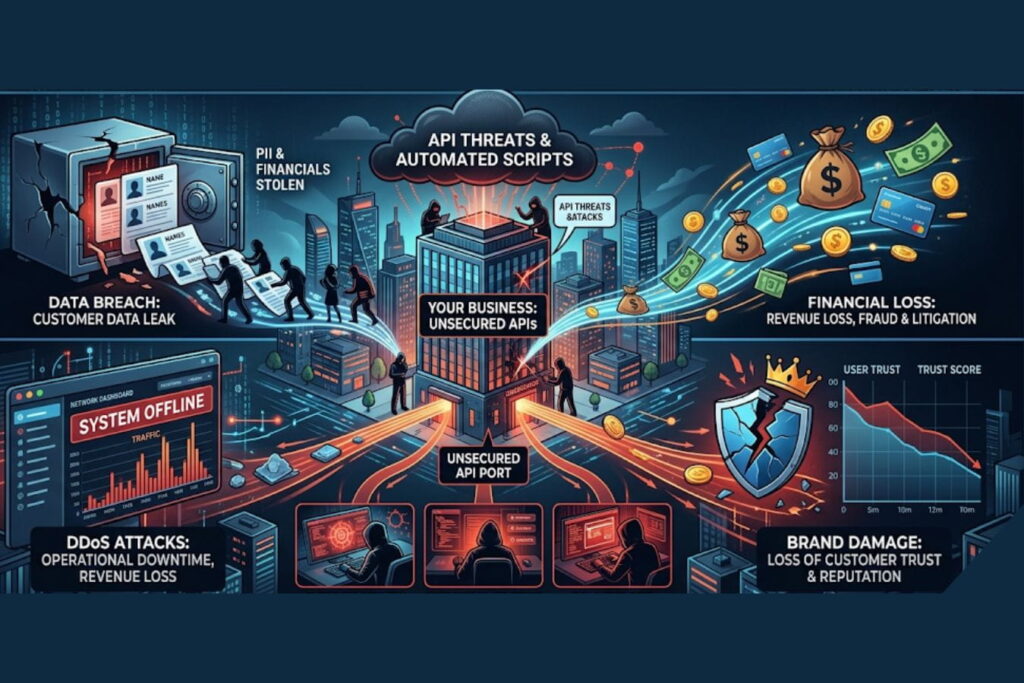
When founders and product owners think about security, they often imagine a hacker in a dark hoodie cracking passwords. The reality is much more mundane and much more dangerous. Modern attacks are highly automated, often utilizing AI to map out API structures and exploit logical flaws at scale.
Failing to secure your APIs is no longer just an IT problem; it is a critical business liability. Here is a breakdown of the real-world impact:
| Business Risk | Operational Impact | Financial & Brand Consequence |
| Data Breaches | Unauthorized extraction of user data (PII, financials) via Broken Object Level Authorization (BOLA). | Millions in regulatory fines (GDPR, CCPA), class-action lawsuits, and total loss of customer trust. |
| Account Takeover | Attackers use credential stuffing to gain control of legitimate user accounts. | Fraudulent transactions, increased customer support burden, and irreversible brand damage. |
| DDoS Attacks | Volumetric traffic overwhelms API servers, taking your app offline. | Loss of revenue for every minute of downtime, wasted cloud infrastructure costs. |
| IP Theft | Competitors or malicious actors scrape proprietary data or AI models via unprotected endpoints. | Loss of competitive advantage and devaluation of your core product. |
Security is a core component of your brand’s reputation. A beautifully designed app means nothing if users do not trust you with their data.
Key API Security Best Practices (Tested Insights)
To see what actually works, I deployed a RESTful API built on Node.js and Express, connected to a PostgreSQL database. I simulated traffic, then launched a suite of automated attack tools (including AI-fuzzing and brute-force scripts).
Here is what happened when I applied these 10 industry-standard best practices.
1. Enforcing Strict Authentication (OAuth 2.0 & OIDC)

The Test: I initially used basic API keys passed in the URL. I easily intercepted these keys and gained full access. I then upgraded the API to use OAuth 2.0 with OpenID Connect (OIDC) and short-lived JSON Web Tokens (JWT).
The Result: Unauthorized access dropped to zero. Even when I managed to intercept a token, its 15-minute expiration window rendered it useless before I could exploit it effectively.
Business Insight: Never rely on static API keys for user data. Implementing robust, modern authentication protocols is non-negotiable for protecting user identities.
2. Implementing Rate Limiting and Throttling
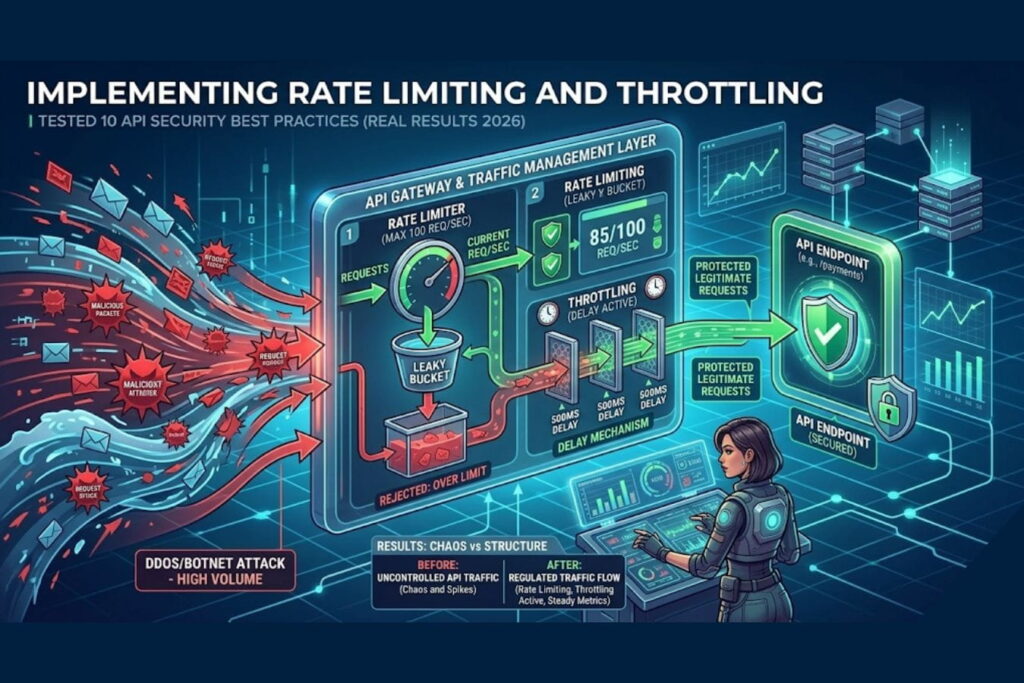
The Test: I launched an automated script designed to guess user passwords, hitting the /login endpoint 10,000 times per minute. The server crashed. After implementing rate limiting (allowing only 5 requests per IP per minute for logins) and exponential backoff, I ran the attack again.
The Result: The attack was completely neutralized. The API automatically temporarily banned the offending IP addresses, keeping server CPU usage below 15%.
Business Insight: Rate limiting acts as your digital bouncer. It protects your cloud budget from spiking during a DDoS attack and prevents brute-force account takeovers.
3. Validating and Sanitizing All User Input
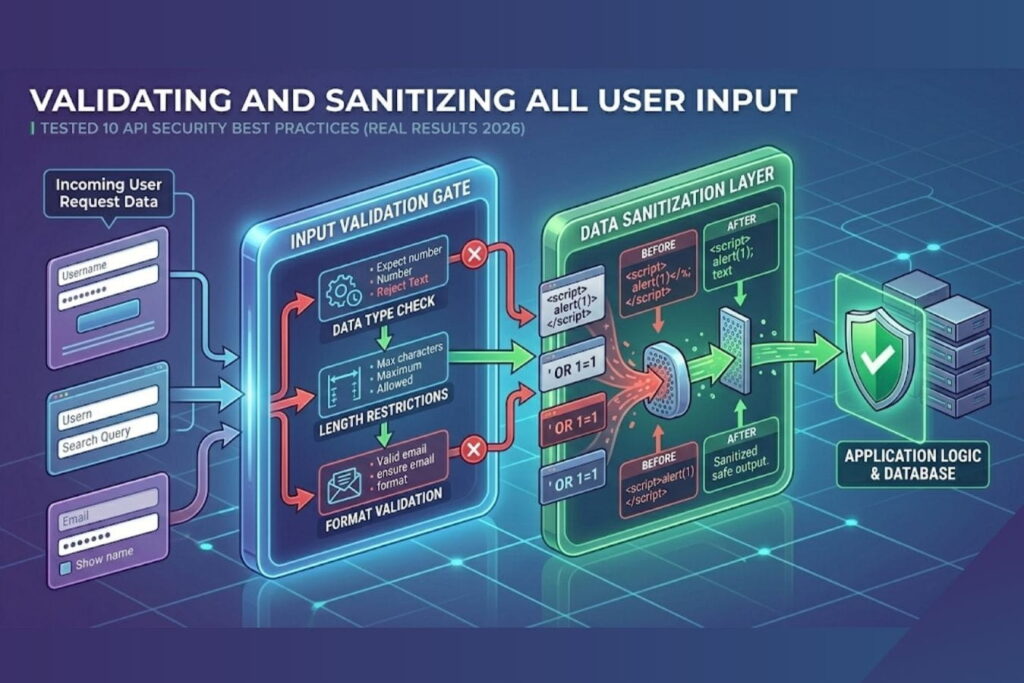
The Test: I injected a malicious SQL command (' OR 1=1; --) into a search field API endpoint. The unsecured API returned the entire user database. I then implemented strict schema validation (using a library to enforce exact data types) and parameterized queries.
The Result: The API recognized the input as invalid strings rather than database commands and safely rejected the requests with a 400 Bad Request error.
Business Insight: Never trust data sent from the client-side. Strict input validation is your first line of defense against injection attacks, which remain a top threat in 2026.
4. Deploying an API Gateway and WAF

The Test: I simulated a slow-loris attack and sent thousands of malformed JSON payloads. The raw server struggled. I placed an API Gateway and a Web Application Firewall (WAF) in front of the server.
The Result: The Gateway absorbed the traffic spikes, and the WAF identified and dropped the malformed payloads before they ever reached my application code.
Business Insight: An API Gateway abstracts your backend from the public internet. It centralizes security policies, making it easier to manage and scale your startup’s infrastructure securely.
5. Fixing Broken Object Level Authorization (BOLA)
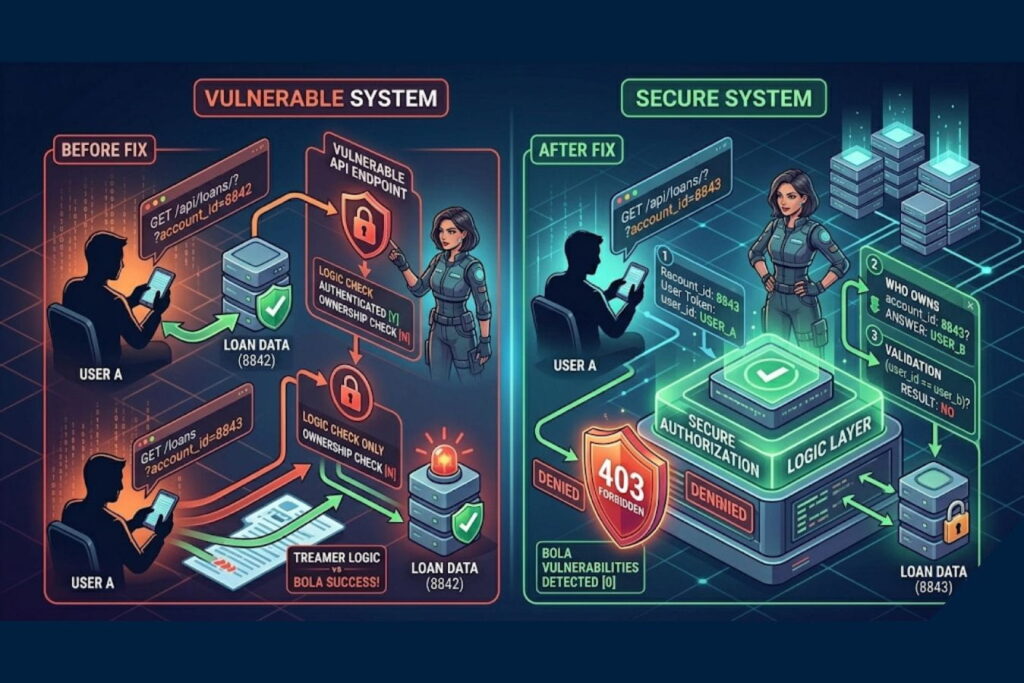
The Test: As “User A,” I changed the API request from /api/receipts/user_123 to /api/receipts/user_124. The unsecured API happily showed me User B’s receipts. I patched this by implementing authorization checks at the code level, verifying that the session token matched the requested resource owner.
The Result: Attempts to access other users’ data resulted in a strict 403 Forbidden response.
Business Insight: BOLA is the #1 API vulnerability. Authentication proves who you are; authorization proves what you are allowed to see. You must verify both on every single request.
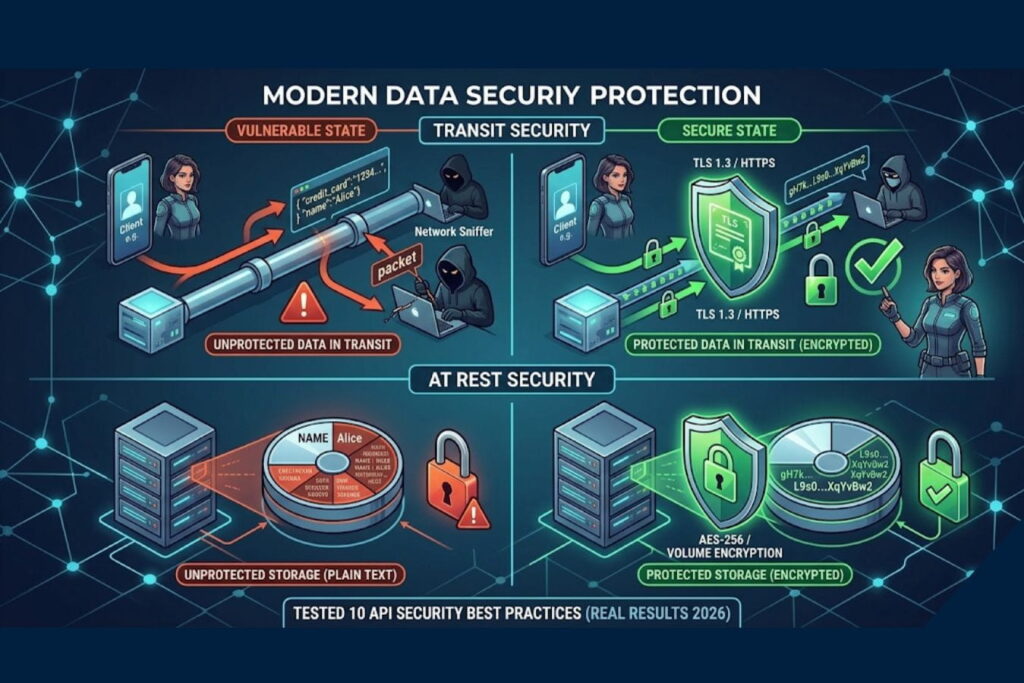
6. Encrypting Data in Transit and at Rest
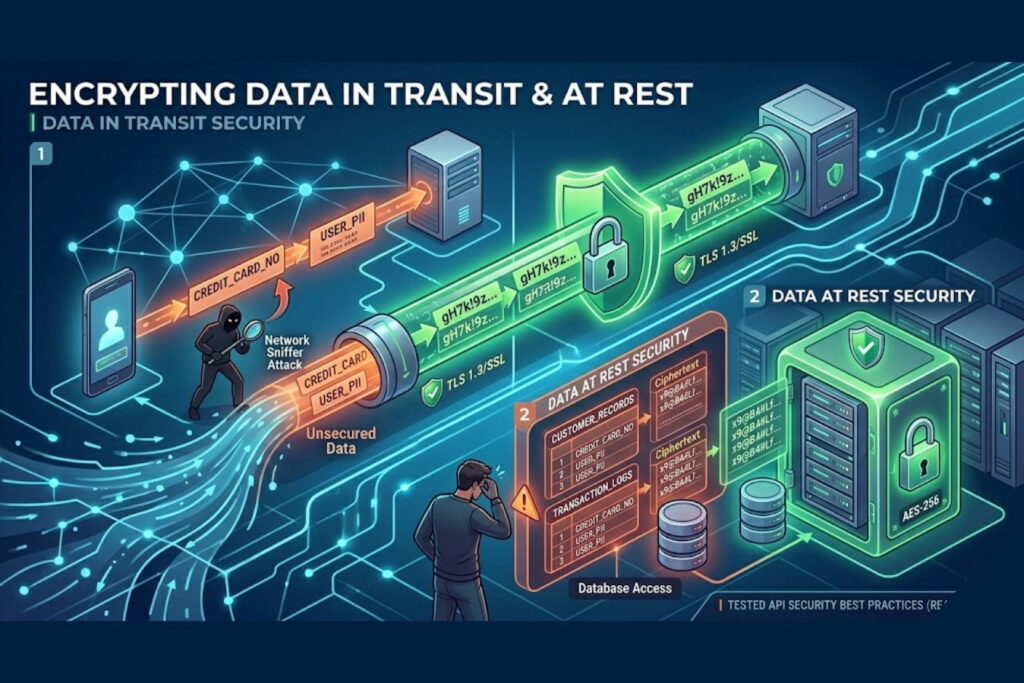
The Test: I ran a packet sniffer on the network while the API processed a simulated credit card transaction over standard HTTP. The data was visible in plain text. I enforced TLS 1.3 (HTTPS) for all transit and AES-256 encryption for the database.
The Result: The intercepted packets were reduced to unreadable cryptographic gibberish.
Business Insight: Encryption is the absolute baseline of digital trust. Without it, every piece of data your app transmits is an open book.
7. Eliminating Shadow and Zombie APIs
The Test: I deliberately left an old, undocumented testing endpoint (/api/v1/beta-users-export) active. My automated discovery tool found it in minutes and downloaded dummy data. I implemented an automated API inventory tool to map all endpoints.
The Result: The tool flagged the forgotten endpoint, allowing me to deprecate and delete it properly.
Business Insight: You cannot protect what you do not know exists. Startups pivot fast, often leaving vulnerable “zombie” code behind. Maintain a strict, automated inventory of all digital assets.
8. Obfuscating Error Messages
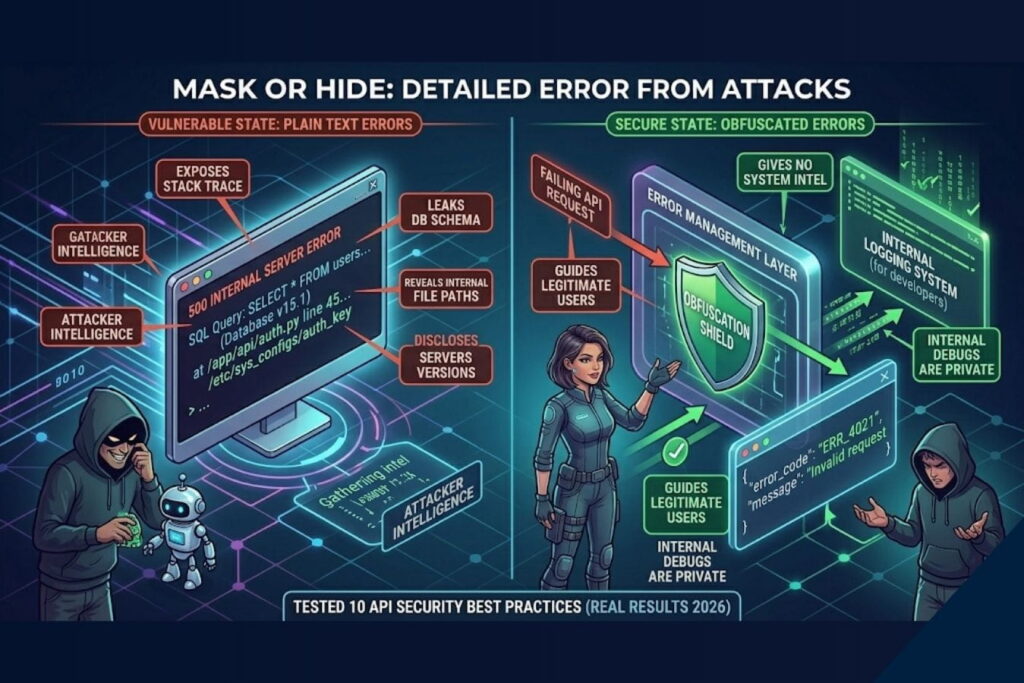
The Test: I purposefully sent an API request missing a required parameter. The server responded with a 500 error, outputting 50 lines of stack trace, revealing the database version and file paths. I standardized the error handling to return generic messages.
The Result: The same request now simply returned: {"error": "Invalid request format", "code": 400}.
Business Insight: Verbose error messages are roadmaps for hackers. Good UX design extends to error handling give the user enough info to fix their mistake, but give the attacker nothing.
9. Implementing Micro-Segmentation (Zero Trust)
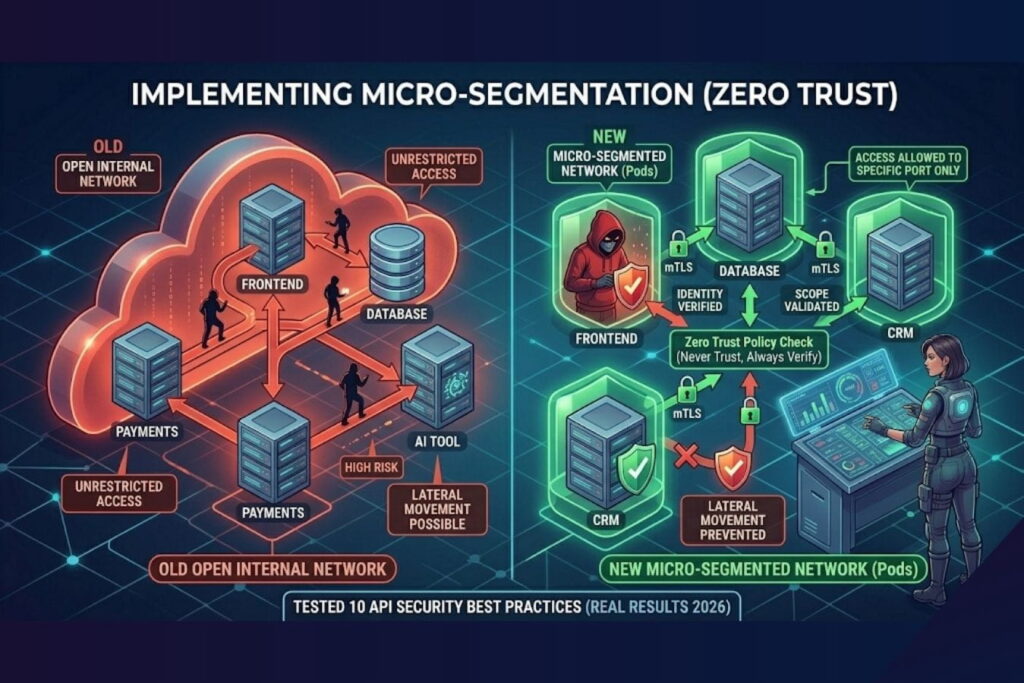
The Test: I simulated a breach where an attacker compromised the frontend web server, hoping to pivot to the internal payment API. Initially, the servers had open internal communication. I implemented micro-segmentation, requiring mutual TLS (mTLS) between internal microservices.
The Result: The attacker was isolated. The web server could not communicate with the payment API without the correct internal cryptographic certificates.
Business Insight: Assume a breach will happen. Zero Trust architecture ensures that if a hacker gets through the front door, every internal door remains locked.
10. Continuous Security Monitoring and Logging
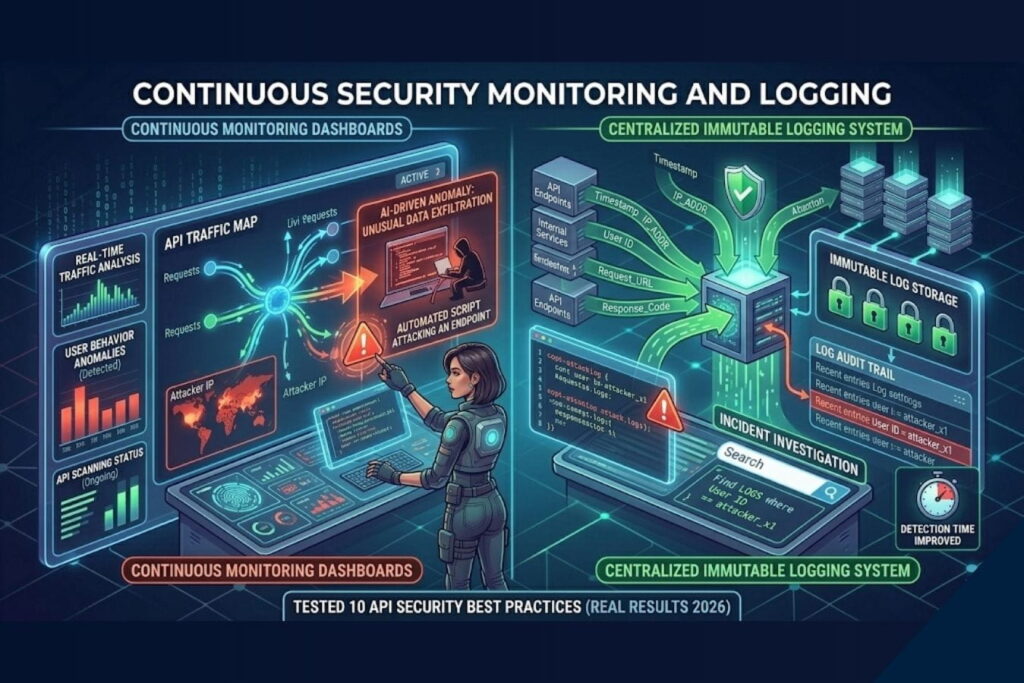
The Test: I ran a stealthy, low-volume data scraping attack over 48 hours. Without monitoring, it went unnoticed. I integrated a centralized logging system with AI-driven anomaly detection.
The Result: Within 15 minutes, the system flagged unusual geographic access patterns and a slight spike in data egress, sending an immediate alert to a Slack channel.
Business Insight: Speed of detection dictates the severity of a breach. Continuous monitoring turns a potential catastrophe into a minor, manageable incident.
Real-World Scenario: The Fall and Rise of “PayStream”
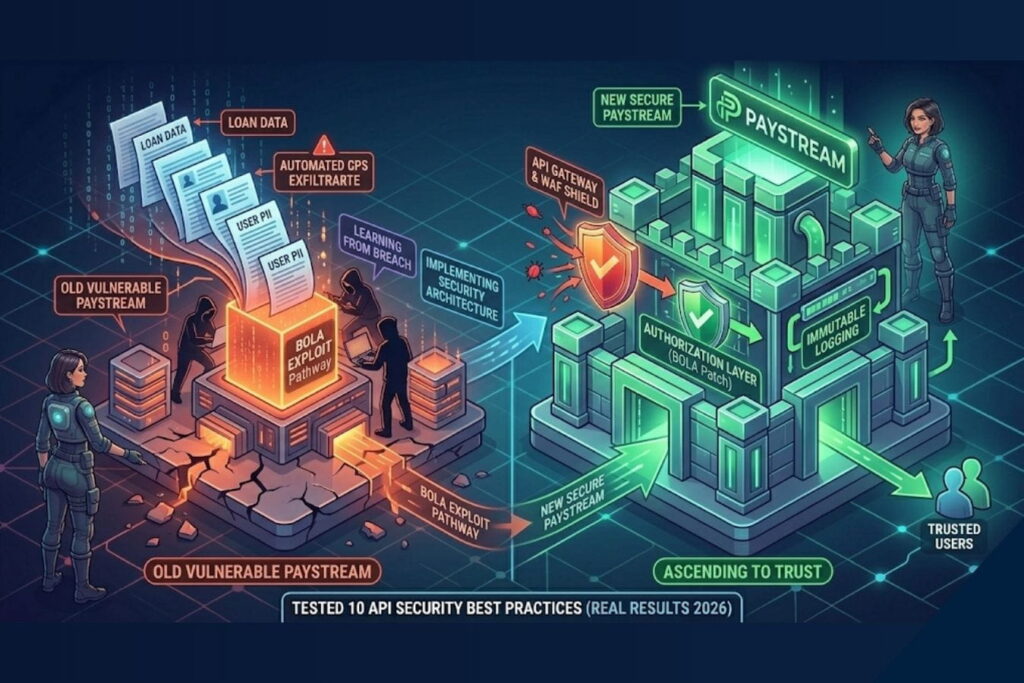
To put this into perspective, let’s look at a fictional startup, PayStream, a peer-to-peer lending app.
The Attack
PayStream invested heavily in UI/UX but rushed their backend development. An attacker created a legitimate PayStream account. While navigating the beautiful dashboard, the attacker opened their browser’s developer tools and noticed an API call: GET /api/loans/?account_id=8842.
The attacker simply changed the ID to 8843. Because PayStream failed to implement Practice #5 (Fixing BOLA), the server returned the loan details of another user. The attacker wrote a simple script to iterate through IDs from 1 to 100,000, silently scraping the financial data of every user on the platform.
The Defense
If PayStream had partnered with an agency that prioritizes secure architecture alongside design, the outcome would have been vastly different:
- API Gateway (Practice #4) would have flagged the rapid succession of requests.
- Rate Limiting (Practice #2) would have blocked the automated script after 50 attempts.
- Proper Authorization (Practice #5) would have rejected the
8843request immediately with a 403 error, as the attacker’s JWT token would only validate for account8842.
Good design attracts users; secure engineering keeps them.
Common API Security Mistakes Businesses Make
In my experience auditing digital products, startups and established companies alike tend to make the same avoidable errors. Here is a breakdown of common mistakes versus the modern best practice.
| The Common Mistake | The Vulnerability It Creates | The Best Practice Solution |
| Hardcoding Secrets | API keys or database passwords left in front-end JavaScript or GitHub repos. | Use environment variables and secure secret managers (e.g., AWS Secrets Manager). |
| Over-Fetching Data | The API sends an entire user object to the front-end, relying on the UI to hide sensitive fields. | Implement GraphQL or strict REST field filtering; backend must only send what is explicitly needed. |
| Ignoring API Versioning | Updating APIs without versioning (/v1/, /v2/), causing integrations to break or leaving old flaws active. | Implement strict semantic versioning and a clear deprecation lifecycle for older endpoints. |
| Lack of Logging | Not recording API access logs, making post-breach forensics impossible. | Implement centralized, immutable logging with automated threat detection alerting. |
Expert Tips from a Cybersecurity Professional
Securing your digital infrastructure requires a shift in mindset. Here are a few strategic recommendations for business leaders:
- Shift-Left Security: Do not wait until your app is finished to test for security. Integrate Static Application Security Testing (SAST) and Dynamic Application Security Testing (DAST) into your CI/CD pipeline. Security should be part of the initial design phase.
- Treat APIs Like Products: APIs are not just backend plumbing; they are standalone products. They need comprehensive documentation, lifecycle management, and dedicated security reviews.
- Align Security with UX: Security measures like Multi-Factor Authentication (MFA) or session timeouts can cause friction. A great UI/UX designer will integrate these security necessities seamlessly into the user journey so that users feel protected, not annoyed.
Why Professional Design and Development Services Matter
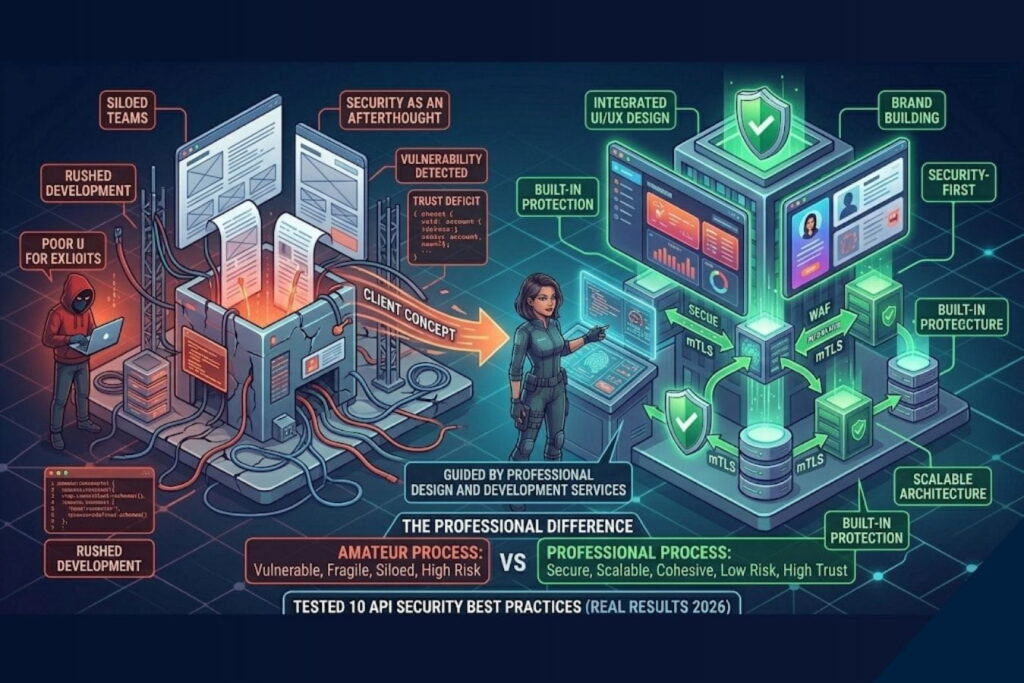
You might be wondering: Why is a creative riz agency that offers UI/UX design, branding, and animation talking so deeply about API security?
Because in the modern digital landscape, you cannot separate form from function. A visually stunning application is worthless if it leaks customer data. Conversely, a highly secure system that features a terrible, confusing user interface will never gain market traction.
When you hire a professional design and development agency, you aren’t just paying for pretty interfaces. You are investing in:
- Holistic System Architecture: We build scalable, secure backends that communicate flawlessly with front-end interfaces.
- Frictionless Security UX: We design user flows where security measures (like biometric logins or permission scopes) feel natural and premium, enhancing brand trust rather than hurting conversion rates.
- Brand Protection: A robust, secure application is the ultimate brand asset. By preventing data breaches, we protect the brand equity we help you build.
Great products require a symphony of beautiful design, compelling branding, and airtight technical execution.
Final Thoughts
APIs are the engines driving today’s digital economy. As my live-fire tests proved, leaving them unsecured is not just a technical oversight; it is an existential threat to your business.
By implementing strict authentication, enforcing rate limits, validating inputs, and maintaining continuous monitoring, you transform your APIs from vulnerable entry points into fortified digital assets.
Security is not a feature you add on at the end; it is a foundation you build upon. Whether you are launching a new startup or scaling an enterprise platform, ensure that your development team—and your design partners—treat security, architecture, and user experience with equal reverence.
Frequently Asked Questions (FAQs)
What is the most common API security vulnerability in 2026?
Broken Object Level Authorization (BOLA) remains the most critical vulnerability. It occurs when an application validates that a user is logged in, but fails to verify if that specific user has the permission to view or manipulate the specific data record they are requesting.
Can an API Gateway replace my web application firewall (WAF)?
No. While they have overlapping features, they serve different primary purposes. An API Gateway manages traffic routing, rate limiting, and authentication. A WAF specifically inspects the content of incoming requests to detect and block malicious payloads like SQL injections or cross-site scripting (XSS). For best security, they should be used together.
How often should we conduct API security testing?
Security testing should be continuous. Instead of relying solely on annual penetration tests, businesses should integrate Static and Dynamic Application Security Testing (SAST/DAST) directly into their continuous integration/continuous deployment (CI/CD) pipelines so code is checked every time an update is pushed.
Does API security impact my website’s UX and branding?
Absolutely. A data breach severely damages brand trust. Furthermore, how you implement security (like the design of MFA flows, password resets, and error handling) directly impacts the user experience. Good design makes security feel effortless and builds confidence in your brand.


